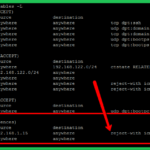
Fail2ban uses iptables by default to block incoming connections when they exceed the max. login retries. The iptables rules used by fail2ban might conflict with other firewall rules, so it might be necessary to reconfigure fail2ban to use the route command for blocking incoming connections.
Fail2ban ban using route command
To reconfigure fail2ban for using the route command instead of iptables, edit or create the route.conf file:
nano /etc/fail2ban/action.d/route.conf
There you insert the following lines:
# Fail2Ban configuration file [Definition] actionban = ip route add unreachableactionunban = ip route del unreachable
Then add or change the ban action in the jail.local file in the [DEFAULT] section to “route”:
nano/etc/fail2ban/jail.local
And add or edit these lines:
# Fail2Ban configuration file [DEFAULT] banaction = route
The post Configure fail2ban to use route instead of iptables to block connections appeared first on FAQforge.
Discover more from Ubuntu-Server.com
Subscribe to get the latest posts sent to your email.